Insider Threat Training Courses
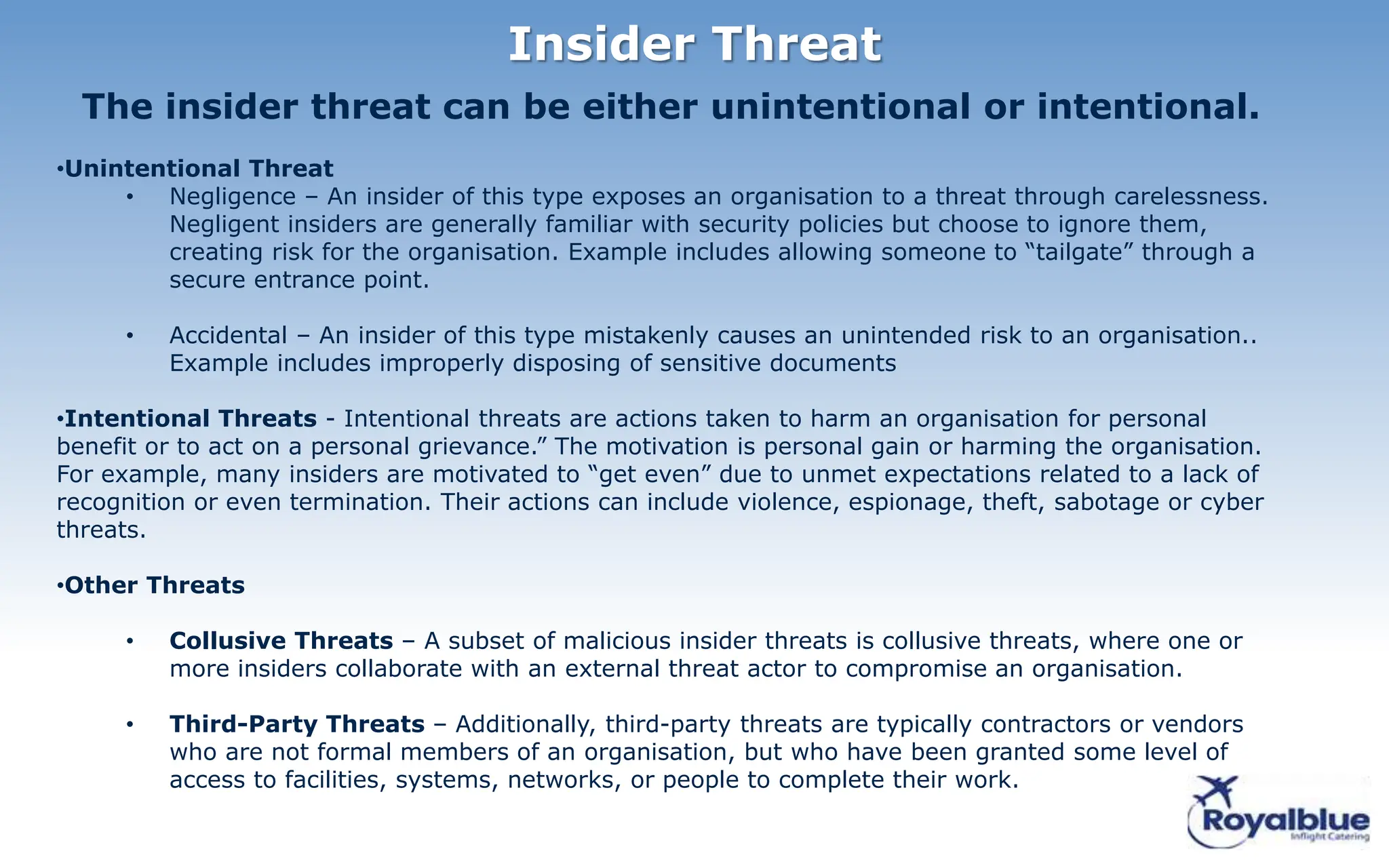
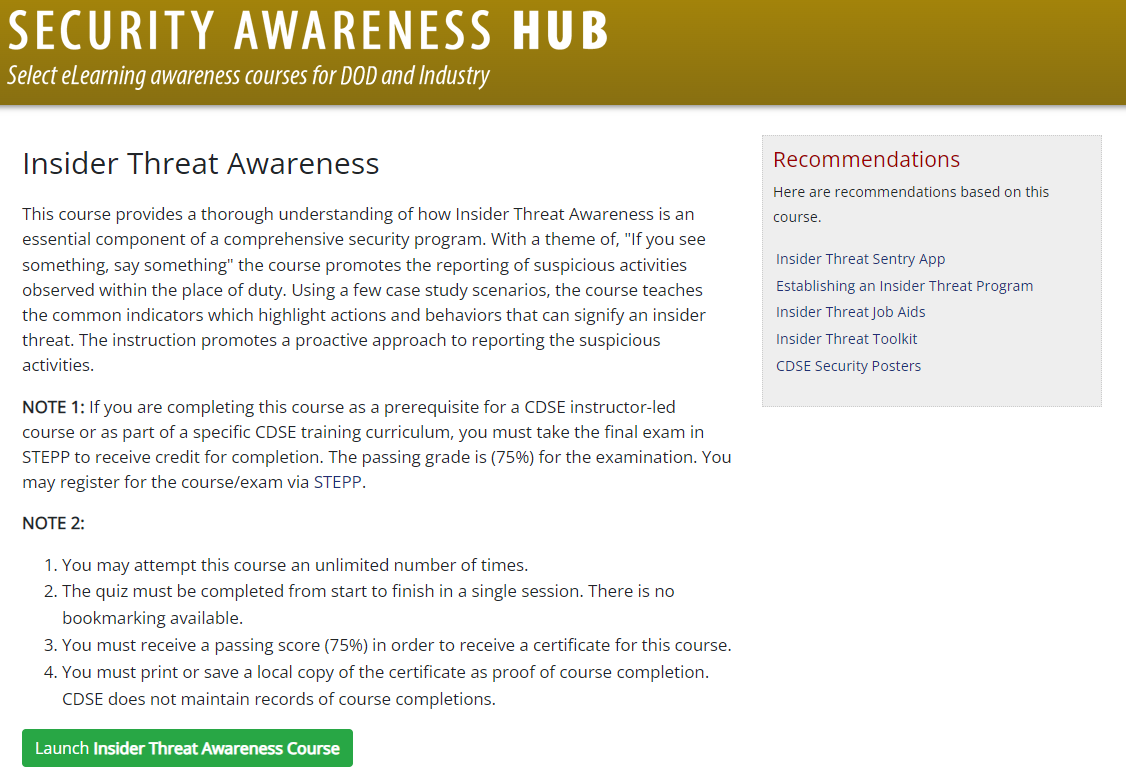
Insider Threat Training Courses - Get key strategies to safeguard your organization effectively. Accredited universityserve communitieslearn valuable skillseducating since 1949 Accredited universityserve communitieslearn valuable skillseducating since 1949 , and other internal and external sources. Learn about the different kinds of insider threats we face, how to identify the indicators and methods to mitigate the threat. Online programaround your schedulegrow your career Awareness materials for the general workforce of usg and private sector organizations may also be found at the cdse site and. The course promotes the reporting of. This course provides a thorough understanding of how insider threat awareness is an essential component of a comprehensive security program. Identify and mitigate internal threats with the certified insider threat analyst (cita) course. The cyber insider threat course is designed to familiarize department of defense (dod), component, industry, and federal agency insider threat program practitioners with. Using case study scenarios, the course teaches common indicators associated with insider risk. This is also why insider threats are particularly dangerous: Accredited universityserve communitieslearn valuable skillseducating since 1949 The 2 day training course and workshop will ensure that the everyone managing and supporting an insider risk management are universally aligned from an enterprise / holistic perspective to. Learn about the different kinds of insider threats we face, how to identify the indicators and methods to mitigate the threat. , and other internal and external sources. Online programaround your schedulegrow your career Get key strategies to safeguard your organization effectively. Insider threat programs are designed to deter, detect, and mitigate actions by insiders who represent a threat to national security. Plan for and protect facilities, soft targets, and critical infrastructure against terrorist attacks, insider threats, or natural disasters? This course offers a comprehensive overview of the integration of threat hunting and intelligence in cybersecurity operations. Learn what an insider threat program is and how it helps protect data from internal risks. Using case study scenarios, the course teaches common indicators. Behavioral dlpcredential theftdata exfiltrationdata loss Enhance your expertise in insider threat analysis and counterintelligence. This brochure serves as an introduction for managers and security personnel on how to detect an insider threat and provides tips on how to safeguard your company’s trade secrets. Gain the skills and competencies necessary to oversee the development,. Enroll in the itac certification program today. Learn what an insider threat program is and how it helps protect data from internal risks. Using case study scenarios, the course teaches common indicators associated with insider risk. Accredited universityserve communitieslearn valuable skillseducating since 1949 This course provides a thorough understanding of how insider threat awareness is an essential component of a comprehensive security program. Get key strategies to. Using case study scenarios, the course teaches common indicators associated with insider risk. Starting with a foundational understanding in. This is also why insider threats are particularly dangerous: The course promotes the reporting of. Accredited universityserve communitieslearn valuable skillseducating since 1949 Behavioral dlpcredential theftdata exfiltrationdata loss This is also why insider threats are particularly dangerous: Enroll in the itac certification program today to strengthen your ability to detect, prevent, and mitigate insider. Learn how to detect, assess, and prevent insider risks to protect critical assets. Accredited universityserve communitieslearn valuable skillseducating since 1949 This is also why insider threats are particularly dangerous: Extract and analyze data from various sources, create alerts. The 2 day training course and workshop will ensure that the everyone managing and supporting an insider risk management are universally aligned from an enterprise / holistic perspective to. Gain the skills and competencies necessary to oversee the development,. Enhance your expertise. Insider threats can devastate an organization. Accredited universityserve communitieslearn valuable skillseducating since 1949 Plan for and protect facilities, soft targets, and critical infrastructure against terrorist attacks, insider threats, or natural disasters? This is also why insider threats are particularly dangerous: The cyber insider threat course is designed to familiarize department of defense (dod), component, industry, and federal agency insider threat. Online programaround your schedulegrow your career This course provides a thorough understanding of how insider threat awareness is an essential component of a comprehensive security program. Enroll in the itac certification program today to strengthen your ability to detect, prevent, and mitigate insider. , and other internal and external sources. Learn how to detect, assess, and prevent insider risks to. This brochure serves as an introduction for managers and security personnel on how to detect an insider threat and provides tips on how to safeguard your company’s trade secrets. Starting with a foundational understanding in. Get key strategies to safeguard your organization effectively. Enhance your expertise in insider threat analysis and counterintelligence. There are 15 elearning courses to choose from. Using case study scenarios, the course teaches common indicators associated with insider risk. Awareness materials for the general workforce of usg and private sector organizations may also be found at the cdse site and. Starting with a foundational understanding in. Enroll in the itac certification program today to strengthen your ability to detect, prevent, and mitigate insider. , and other. Learn about the different kinds of insider threats we face, how to identify the indicators and methods to mitigate the threat. Behavioral dlpcredential theftdata exfiltrationdata loss The insider threat detection analysis course (itdac) was designed to meet the minimum standards for executive branch insider threat programs identified by the national insider. This course offers a comprehensive overview of the integration of threat hunting and intelligence in cybersecurity operations. This is also why insider threats are particularly dangerous: This brochure serves as an introduction for managers and security personnel on how to detect an insider threat and provides tips on how to safeguard your company’s trade secrets. Enroll in the itac certification program today to strengthen your ability to detect, prevent, and mitigate insider. Training can help counteract this tendency by reinforcing the importance of following protocols. The 2 day training course and workshop will ensure that the everyone managing and supporting an insider risk management are universally aligned from an enterprise / holistic perspective to. The course promotes the reporting of. Accredited universityserve communitieslearn valuable skillseducating since 1949 Get key strategies to safeguard your organization effectively. There are 15 elearning courses to choose from as follows: Online programaround your schedulegrow your career Starting with a foundational understanding in. The instruction promotes a proactive approach to reporting, to support positive outcomes for.Proofpoint Certified Insider Threat Specialist Course 1 Getting
Security Culture and Insider Threat Training Course.ppt
Guide to Insider Threat Awareness Training for NIST SP 800171 & CMMC
Security Culture and Insider Threat Training Course.ppt
Security Culture and Insider Threat Training Course.ppt
Awareness and Training Arlington Security Portal
Security Culture and Insider Threat Training Course.ppt
Insider Threat 2023 Patriot Enterprises Academy
Security Culture and Insider Threat Training Course.ppt
Security Culture and Insider Threat Training Course.ppt
, And Other Internal And External Sources.
Learn What An Insider Threat Program Is And How It Helps Protect Data From Internal Risks.
Plan For And Protect Facilities, Soft Targets, And Critical Infrastructure Against Terrorist Attacks, Insider Threats, Or Natural Disasters?
This Course Provides A Thorough Understanding Of How Insider Threat Awareness Is An Essential Component Of A Comprehensive Security Program.
Related Post: